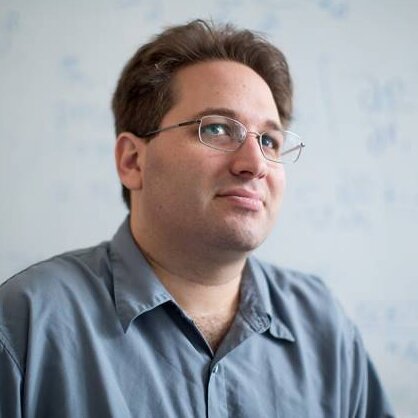
Radu Sion

Radu Sion is a professor at Stony Brook University (on leave), the director of the National Security Institute, and the CEO of Private Machines Inc. Sion’s research is in cyber security and large-scale computing. He has published 85-plus peer-reviewed works in top venues and has organized 65-plus conferences. Sion has received the National Science Foundation Career Award for his work on cloud computing security. He has worked with and received funding from numerous industry and government partners, including the US Air Force, the Office of the Secretary of Defense, the Department of Homeland Security, the US Army, the Intelligence ARPA, the Office of Naval Research, Northrop Grumman, IBM, Nokia, Motorola, Xerox Parc, Microsoft, SAP, CA Technologies, the National Science Foundation, and many others. Sion is currently leading Private Machines Inc., a cyber security startup designing next-generation secure cloud computing technologies.






 Share
Share